
INTRODUCTION:
When we send our important/sensitive data over internet (example: login credentials on Banking site) we don’t want our details to be downloaded by some Man in the Middle and only intended recipient can understand it.
This is important because the information we send on the Internet is passed from computer to computer to get to the destination server. Any computer in between you and the server can see your credit card numbers, usernames and passwords, and other sensitive information if it is not encrypted with an TLS/SSL certificate.
Transport Layer Security (TLS), and Secure Sockets Layer (SSL), are cryptographic protocols designed to provide communications security over a computer network or Internet. (eg: HTTPS)
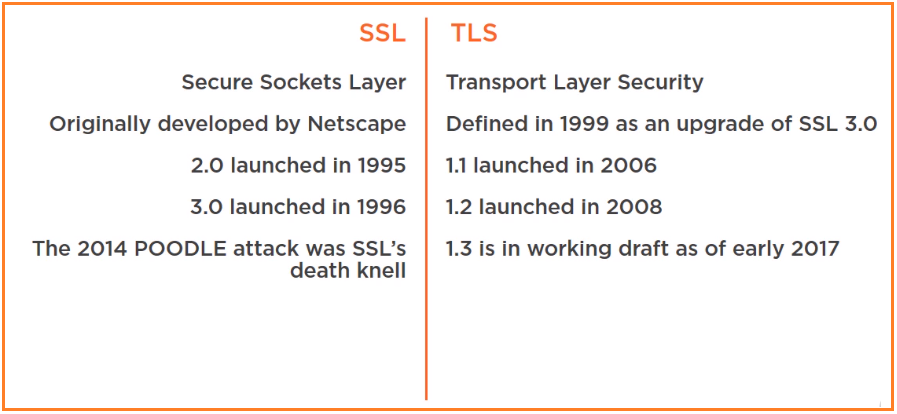
SSL is the older encryption protocol & TLS is new one but now days people often say SSL when they mean to say TLS.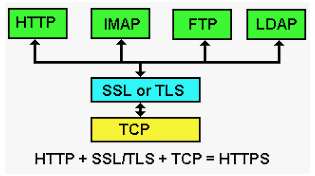
DIFFERENCE BETWEEN SSL & TLS
TLS (Transport layer security)
The TLS protocol aims primarily to provide privacy and data integrity between two or more communicating computer applications. When secured by TLS, connections between a client (e.g., a web browser) and a server (e.g., wikipedia.org) should have one or more of the following properties:
- The connection is private (or secure) because symmetric cryptography is used to encrypt the data transmitted.
- The identity of the communicating parties can be authenticated using public-key cryptography.
- The connection is reliable because each message transmitted includes a message integrity check using a message authentication code to prevent undetected loss or alteration of the data during transmission.
TLS HANDSHAKE:
When client wants to connect with server on browser on HTTPS, they tend to connect with TLS.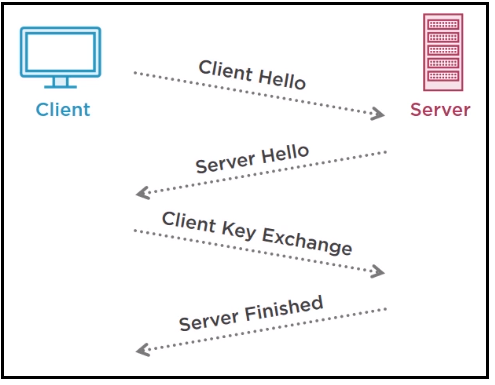
- Communication starts with client sending a client HELLO. And within this request client communicates things such as highest level of TLS support. Also supported cipher switches in order of preference of its use.
- SERVER respond with Server HELLO and in this response it rely on protocol version and cipher switch as well as providing it’s public key back to the client.
- Client can verify the public key against list of verified CA’s. (confidentiality of Authentic server).
- This initial communication is yet not encrypted, it is just negotiation phase.
- The client now perform key exchange with server, and this response is encrypted with server public key.
- For this server responds with SERVER FINISHED response.
SSL (Secure Socket Layer):
The (SSL) protocol was created by Netscape chief scientist Taher Elgamal to ensure secure transactions between web servers and browsers. Its first commercial version 2.0 was launched in 1995. version 1.0 was never launched officially.
The usage of SSL technology ensures that all data transmitted between the web server and browser remains encrypted.
SSL provides a secure channel between two machines or devices operating over the internet or an internal network. One common example is when SSL is used to secure communication between a web browser and a web server. This turns a website’s address from HTTP to HTTPS, the ‘S’ standing for ‘secure’.
End of SSL
In 2014, SSL 3.0 was found to be vulnerable to the POODLE attack that affects all block ciphers in SSL and SSL reached it’s end of life.
SSL 2.0 was prohibited in 2011 by RFC 6176, and SSL 3.0 was also later prohibited in June 2015 by RFC 7568.
*——————————————————————————————————————*
Hopefully this document will be helpful and easy in understanding the concept. In further blogs we will use different methods to encrypt web pages using different methods. Thanks for reading this 🙂
Want to explore about Certificate more, read following article:
https://learningtechnix.wordpress.com/2018/10/09/openssl-creating-self-sign-certificates/
Appreciate you sharing, great blog.Really thank you! Want more.
LikeLike
Fantastic post. Fantastic.
LikeLike
Great blog post.Really looking forward to read more. Fantastic.
LikeLike
Major thankies for the post.
LikeLike
Im grateful for the blog post. Great.
LikeLike
It’s like you read my thoughts! You’ve made my day! Thx again. I enjoyed reading what you had to say. You’ve made my day! Thx again.
LikeLike
I enjoyed reading this. Interesting content. I have been looking everywhere for this! Thumbs up!
LikeLike
I enjoyed reading what you had to say. Good job on this article! It’s like you wrote the book on it or something. I enjoyed your post. Thank you.
LikeLike
You are so interesting! I don’t believe I’ve read through anything like this before. So nice to find somebody with unique thoughts on this subject matter. Seriously.. many thanks for starting this up. This website is one thing that is needed on the web, someone with a bit of originality!
LikeLike
Thanks again for the blog.Thanks Again. Will read on…
LikeLike
Great, thanks for sharing this blog post.Really looking forward to read more. Fantastic.
LikeLike
This website was… how do you say it? Relevant!! Finally I’ve found something which helped me. Cheers!
LikeLike
Aw, this was an exceptionally nice post. Taking a few minutes and actual effort to generate a top notch article… but what can I say… I put things off a whole lot and don’t seem to get anything done.
LikeLike
ehternet cables are still the ones that i use for my home networking applications,
LikeLike
Same here ☺️
LikeLike
This is a topic that is close to my heart… Thank you! Where are your contact details though?
LikeLike
Saved as a favorite, I like your website!
LikeLike
Very good article! We will be linking to this great post on our site. Keep up the good writing.
LikeLike
This is the right site for everyone who really wants to understand this topic. You realize so much its almost hard to argue with you (not that I really would want toÖHaHa). You definitely put a new spin on a subject that’s been written about for ages. Great stuff, just excellent!
LikeLike
I love it when individuals get together and share ideas. Great site, continue the good work!
LikeLike
I need to to thank you for this fantastic read!! I definitely loved every bit of it. I have you book marked to look at new things you postÖ
LikeLike